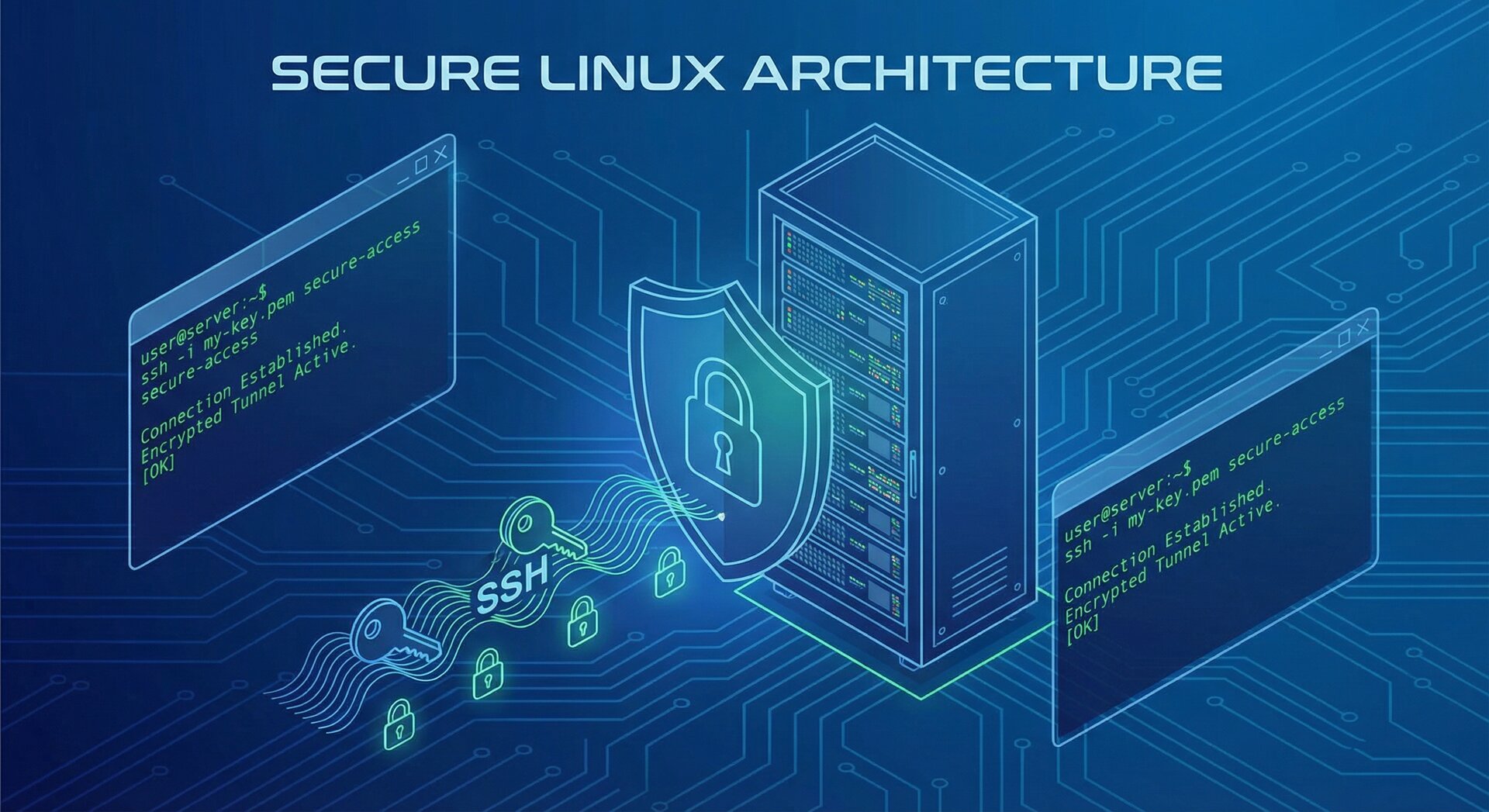
Linux SSH Server Hardening: Complete Security Guide (2026)
Linux SSH server hardening is essential for protecting your Ubuntu and Debian servers from brute-force attacks, unauthorized access, and emerging security threats. In March 2026, new vulnerabilities like CVE-2026-2645 in cryptographic libraries and Ed25519 signature verification flaws have made proper SSH configuration more critical than ever. This comprehensive guide covers every aspect of securing your SSH service, from key-based authentication to advanced firewall rules.
Why SSH Server Hardening Matters in 2026
SSH (Secure Shell) remains the primary attack vector for Linux servers. Recent security advisories from Ubuntu (USN-8094-4, USN-8125-1, USN-8126-1) addressed over 1,600 kernel vulnerabilities collectively across Ubuntu 20.04 LTS through 25.10. The Linux SSH server hardening techniques in this tutorial protect against these threats while ensuring compliance with modern security standards.
Unsecured SSH servers face constant brute-force attempts, with attackers using automated tools to guess passwords. A properly hardened SSH configuration eliminates password-based authentication, restricts access to specific users, and implements cryptographic best practices that prevent unauthorized access even if vulnerabilities are discovered.
Step 1: Generate Ed25519 SSH Keys
The foundation of Linux SSH server hardening starts with modern cryptographic key pairs. Ed25519 offers superior security and performance compared to older RSA keys. Generate your key pair on your local machine before configuring the server:
This command creates a secure Ed25519 key pair specifically for production servers. The private key remains on your local machine, while you will copy the public key to your server. Never share your private key or store it on remote systems.
Copy the public key to your server using the ssh-copy-id utility:
Test the key-based login before proceeding. You should authenticate without entering a password. If successful, you are ready to disable password authentication entirely, a critical step in Linux SSH server hardening.
Step 2: Configure SSH Daemon Settings
Edit the SSH configuration file to implement security hardening. Always keep an active SSH session open while making changes, and test new configurations in a separate terminal before closing your original connection:
Add or modify these essential security directives for comprehensive Linux SSH server hardening:
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
PermitRootLogin no
# Disable password authentication
PasswordAuthentication no
PubkeyAuthentication yes
AuthenticationMethods publickey
# Change default SSH port (optional but recommended)
Port 2222
# Allow only specific users
AllowUsers yourusername
# Use only protocol 2
Protocol 2
# Strong ciphers only
Ciphers [email protected],[email protected],[email protected]
# Secure MAC algorithms
MACs [email protected],[email protected]
# Secure key exchange algorithms
KexAlgorithms [email protected],diffie-hellman-group16-sha512
After saving the configuration, validate the syntax and restart the SSH service:
2
sudo systemctl restart sshd
The configuration test command checks for syntax errors before applying changes. Never restart SSH without testing, as a broken configuration could lock you out of your server. This careful approach is essential for successful Linux SSH server hardening.
Step 3: Implement Two-Factor Authentication
For maximum security, add two-factor authentication (2FA) to your SSH access. This ensures that even if your private key is compromised, an attacker cannot access your server without the second authentication factor. Install Google Authenticator PAM module:
2
sudo apt install libpam-google-authenticator
Run the configuration utility as your non-root user to generate a secret key and QR code:
Answer yes to all prompts for maximum security: time-based tokens, updating the .google_authenticator file, disallowing multiple uses of the same token, and enabling rate limiting. Scan the displayed QR code with your authenticator app.
Configure PAM to require the authenticator by editing the SSH PAM configuration:
Add this line after the existing auth directives:
Update your sshd_config to enable challenge-response authentication:
2
AuthenticationMethods publickey,keyboard-interactive
Restart SSH and test the new configuration in a separate terminal. You will now need both your SSH key and a time-based one-time password to authenticate. This multi-layer approach exemplifies proper Linux SSH server hardening.
Step 4: Configure UFW Firewall Rules
A properly configured firewall blocks unauthorized access attempts before they reach your SSH service. UFW (Uncomplicated Firewall) provides an easy-to-use interface for iptables on Ubuntu and Debian systems. Install and configure UFW as part of your Linux SSH server hardening strategy:
2
sudo apt install ufw
Set default policies that deny incoming connections while allowing outgoing traffic:
2
sudo ufw default allow outgoing
Before enabling the firewall, add rules for SSH access. If you changed the default port, specify it explicitly:
Also allow standard web ports if your server hosts websites:
2
sudo ufw allow 443/tcp
Enable rate limiting for SSH to prevent brute-force attacks:
Activate the firewall:
Verify your rules and test connectivity before closing your current SSH session. The status command shows all active rules:
Step 5: Install and Configure Fail2Ban
Fail2Ban provides automated protection against brute-force attacks by monitoring log files and banning IP addresses that show malicious behavior. This essential tool complements your Linux SSH server hardening efforts with dynamic threat response capabilities.
Install Fail2Ban on your Ubuntu or Debian server:
2
sudo systemctl enable --now fail2ban
Create a local configuration file to customize protection settings:
Add these optimized settings for SSH protection:
2
3
4
5
6
7
8
9
10
11
12
13
bantime = 3600
findtime = 600
maxretry = 3
ignoreip = 127.0.0.1/8 ::1 192.168.1.0/24
[sshd]
enabled = true
port = 2222
filter = sshd
logpath = /var/log/auth.log
maxretry = 3
bantime = 3600
These settings ban IP addresses for one hour after three failed login attempts within ten minutes. The ignoreip directive prevents banning your own trusted networks. Adjust these values based on your security requirements and user behavior patterns.
Restart Fail2Ban to apply the configuration:
Monitor the status of SSH protection to ensure it is working correctly:
Step 6: Disable Unnecessary Services
Reducing your server’s attack surface is a fundamental principle of Linux SSH server hardening. Every running service represents a potential entry point for attackers. Audit and disable services that are not required for your server’s function.
List all running services to identify potential targets for removal:
Common services to evaluate for removal on minimal servers include:
- cups (printing service)
- avahi-daemon (mDNS/DNS-SD)
- bluetooth (if not needed)
- ModemManager (if no modems)
- snapd (if not using snap packages)
Disable unnecessary services:
Research each service before disabling to ensure it is not required by your applications. Document all changes for future reference and rollback procedures.
Step 7: Keep Your System Updated
Security patches address newly discovered vulnerabilities promptly. A critical component of Linux SSH server hardening is maintaining an up-to-date system. Configure automatic security updates while maintaining control over major package changes:
2
sudo apt upgrade -y
Install unattended-upgrades for automatic security patching:
2
sudo dpkg-reconfigure unattended-upgrades
Configure unattended-upgrades to automatically install security updates:
Ensure the security update lines are uncommented:
Testing Your Hardened SSH Configuration
After implementing these Linux SSH server hardening measures, thoroughly test your configuration. Attempt to connect from a new terminal session before closing your original connection. Verify that:
- Password authentication is rejected
- Key-based authentication works
- Root login is denied
- Two-factor authentication prompts appear (if configured)
- Firewall rules block unauthorized ports
- Fail2Ban bans IP addresses after failed attempts
Use the SSH verbose mode to debug connection issues:
Conclusion
Linux SSH server hardening is not a one-time task but an ongoing process. Regularly review your security configuration, monitor logs for suspicious activity, and stay informed about new vulnerabilities affecting SSH and related components. The steps in this guide provide a robust foundation for securing your Ubuntu or Debian server against the most common attack vectors in 2026.
Combine these SSH hardening techniques with broader server security practices including network segmentation, regular backups, and intrusion detection systems for comprehensive protection. Your hardened SSH configuration now provides strong authentication, encrypted communications, and automated threat response capabilities that protect your server against evolving security threats.
For more Linux security tutorials, explore our guides on UFW firewall configuration and Fail2Ban setup. Additional resources include the CyberCiti Linux security guide and CentOS SSH hardening documentation.
- About the Author
- Latest Posts
Mark is a senior content editor at Text-Center.com and has more than 20 years of experience with linux and windows operating systems. He also writes for Biteno.com