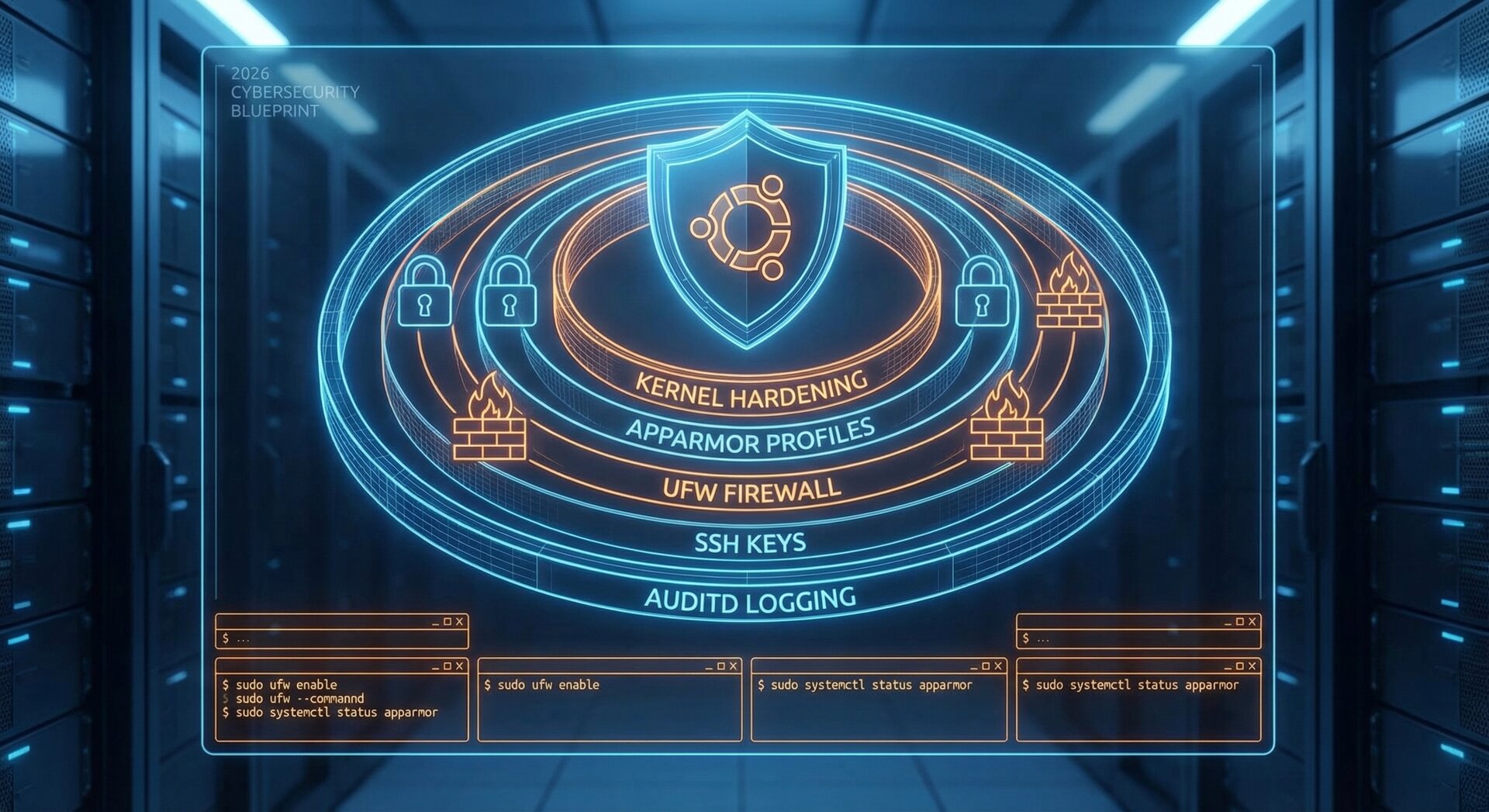
Ubuntu Security Hardening 2026: Complete Guide to Protect Your Linux Server
In 2026, ubuntu security hardening 2026 has become more critical than ever. With kernel exploits, ransomware attacks, and sophisticated threats targeting Linux servers, implementing comprehensive security measures is no longer optional—it’s mandatory. This guide walks you through the essential steps for ubuntu security hardening 2026, covering kernel protections, access controls, firewall configuration, and automated monitoring to keep your Ubuntu server secure.
Why Ubuntu Security Hardening Matters in 2026
Ubuntu servers power millions of websites, applications, and cloud infrastructures worldwide. As cyber threats evolve, attackers increasingly target Linux systems with advanced techniques like Return-Oriented Programming (ROP) attacks, kernel exploits, and privilege escalation. Ubuntu security hardening 2026 addresses these threats through modern kernel features, mandatory access controls, and automated patching strategies.
According to recent security reports, unpatched Linux servers remain the primary attack vector for data breaches. The good news? Ubuntu offers robust tools like Ubuntu Security Guide (USG), Canonical Livepatch, and built-in compliance frameworks (CIS benchmarks, DISA-STIG) that make ubuntu security hardening 2026 achievable even for small teams.
Kernel Hardening: Your First Line of Defense
The Linux kernel is the foundation of your Ubuntu server’s security. In 2026, kernel hardening focuses on three critical areas:
1. Shadow Stack Support (CET)
Control-flow Enforcement Technology (CET) provides hardware-level protection against ROP attacks. Enable Shadow Stack support in Linux Kernel 6.x to prevent attackers from hijacking program execution flow:
2
echo "kernel.shadow_stack=1" | sudo tee -a /etc/sysctl.conf
This feature is essential for ubuntu security hardening 2026 as it blocks entire classes of memory corruption exploits.
2. Kernel Lockdown Mode
Lockdown Mode prevents unsigned kernel modules and debugging access, crucial for production servers:
2
echo "kernel.lockdown=confidentiality" | sudo tee -a /etc/sysctl.conf
This setting blocks direct memory access and kernel debugging interfaces, significantly improving your ubuntu security hardening 2026 posture.
3. Memory Sanitization
Configure the kernel to clear sensitive data after use:
2
3
4
sudo sysctl -w kernel.dmesg_restrict=1
echo "kernel.kptr_restrict=2" | sudo tee -a /etc/sysctl.conf
echo "kernel.dmesg_restrict=1" | sudo tee -a /etc/sysctl.conf
For real-time kernel exploit detection, deploy LKRG (Linux Kernel Runtime Guard). LKRG monitors kernel integrity and detects exploit attempts in real-time, making it a cornerstone of modern ubuntu security hardening 2026 strategies.
Automated Patching with Canonical Livepatch
One of the biggest advantages in ubuntu security hardening 2026 is Canonical Livepatch, which applies kernel security patches without requiring reboots. This is critical for production servers where uptime matters:
2
sudo canonical-livepatch enable YOUR_TOKEN
Get your free token at Ubuntu Livepatch Portal. Livepatch works for Ubuntu 16.04 LTS and later, automatically applying CVE fixes as they’re released.
Combine Livepatch with daily automated updates:
2
sudo dpkg-reconfigure -plow unattended-upgrades
Mandatory Access Controls: AppArmor vs SELinux
Moving beyond traditional file permissions, ubuntu security hardening 2026 requires mandatory access control (MAC) systems. Ubuntu offers two options:
AppArmor (Recommended for Most Users)
AppArmor is enabled by default on Ubuntu and uses path-based confinement policies. It’s simpler to configure than SELinux while providing robust protection:
2
3
sudo aa-enforce /etc/apparmor.d/usr.sbin.nginx # Enforce specific profile
sudo aa-genprof /usr/bin/myapp # Generate profile for custom app
Start with complain mode to test policies without blocking legitimate operations, then switch to enforce mode once tuned.
SELinux (For Fine-Grained Control)
For enterprise environments requiring granular policies, enable SELinux:
2
3
sudo selinux-activate
sudo setenforce 1 # Enforcing mode
SELinux provides more detailed control but requires deeper expertise. Choose the MAC system that fits your team’s skills while pursuing ubuntu security hardening 2026.
Firewall Configuration: ufw and firewalld
Ubuntu’s Uncomplicated Firewall (ufw) provides simple firewall management:
2
3
4
5
6
7
sudo ufw default deny incoming
sudo ufw default allow outgoing
sudo ufw allow 22/tcp # SSH
sudo ufw allow 80/tcp # HTTP
sudo ufw allow 443/tcp # HTTPS
sudo ufw status verbose
For more advanced zone-based configurations, consider firewalld:
2
3
4
sudo firewall-cmd --permanent --zone=public --add-service=ssh
sudo firewall-cmd --permanent --zone=public --add-service=http
sudo firewall-cmd --reload
Proper firewall configuration is fundamental to ubuntu security hardening 2026, blocking unauthorized access attempts before they reach your applications.
Intrusion Detection with Fail2Ban
Fail2Ban automatically blocks IP addresses after repeated failed login attempts:
2
3
sudo systemctl enable fail2ban
sudo systemctl start fail2ban
Configure SSH protection in
1 | /etc/fail2ban/jail.local |
:
2
3
4
5
6
7
enabled = true
port = 22
filter = sshd
logpath = /var/log/auth.log
maxretry = 3
bantime = 3600
Restart Fail2Ban after configuration changes:
For deeper network analysis, add Snort or Suricata for IDS/IPS capabilities, complementing your ubuntu security hardening 2026 efforts.
Monitoring and Auditing Tools
Effective ubuntu security hardening 2026 requires continuous monitoring:
Auditd for System Call Tracking
2
3
4
sudo systemctl enable auditd
sudo auditctl -w /etc/passwd -p wa -k passwd_changes
sudo auditctl -w /etc/shadow -p wa -k shadow_changes
View audit logs:
Tripwire for File Integrity Monitoring
2
3
sudo tripwire --init # Initialize database
sudo tripwire --check # Run integrity check
Lynis Security Auditing
Lynis performs comprehensive security audits and provides actionable recommendations:
2
sudo lynis audit system
Review the report in
1 | /var/log/lynis.log |
and address high-priority findings to improve your ubuntu security hardening 2026 score.
Ubuntu Security Guide (USG) Automation
The Ubuntu Security Guide automates hardening based on CIS and DISA-STIG benchmarks:
2
sudo usg fix cis_level1_server
This single command applies dozens of security settings aligned with industry standards, making ubuntu security hardening 2026 accessible to teams of any size. USG is available from Ubuntu 20.04 LTS onward.
Full Disk Encryption (FDE)
Protect data at rest with LUKS encryption during Ubuntu installation. For existing systems, encrypt additional drives:
2
3
sudo cryptsetup luksOpen /dev/sdb encrypted_drive
sudo mkfs.ext4 /dev/mapper/encrypted_drive
Add to
1 | /etc/crypttab |
for automatic mounting.
Ubuntu Pro: Extended Security Maintenance
Ubuntu Pro extends security patching to the Universe repository and provides FIPS-certified cryptography:
2
3
sudo ua enable esm-infra
sudo ua enable fips
Ubuntu Pro is free for personal use (up to 5 machines) and offers 10 years of security updates, essential for long-term ubuntu security hardening 2026 planning.
Implementation Phases
Follow this phased approach for successful ubuntu security hardening 2026:
- Assessment Phase: Run Lynis audit, check kernel version and patches, identify exposed services with
1nmap
- Hardening Phase: Update kernel, configure AppArmor/SELinux, enable ufw/firewalld, deploy Fail2Ban, install monitoring tools
- Optimization Phase: Automate patching, schedule regular scans, simulate attacks (penetration testing), tune MAC policies
- Maintenance Phase: Monitor MTTD/MTTR metrics, review USN alerts, update incident response playbooks
Common Challenges and Solutions
Teams implementing ubuntu security hardening 2026 often face these obstacles:
- Complexity: Start with AppArmor instead of SELinux; use USG for automated configuration
- Performance Overhead: Enable features selectively; test in staging first
- False Positives: Run MAC systems in complain mode initially; tune based on logs
- Patch Delays: Use Canonical Livepatch and LKRG for interim protection
Conclusion
Implementing ubuntu security hardening 2026 is a continuous process, not a one-time task. By enabling modern kernel protections like Shadow Stack, deploying mandatory access controls with AppArmor or SELinux, configuring automated patching with Canonical Livepatch, and monitoring your systems with Auditd and Lynis, you build multiple layers of defense against evolving threats.
Start with the assessment phase using Lynis, then systematically work through kernel hardening, access controls, firewall setup, and monitoring. Ubuntu Security Guide and Ubuntu Pro significantly reduce the manual effort required, making enterprise-grade ubuntu security hardening 2026 accessible to organizations of all sizes.
Remember: security is a journey. Stay informed about Ubuntu Security Notices, participate in security communities, and continuously improve your hardening practices. Your 2026 Ubuntu server security depends on the measures you implement today.
For more Linux server guides, check out our tutorials on Linux Server Optimization and SSH Key Authentication Setup.
- About the Author
- Latest Posts
Mark is a senior content editor at Text-Center.com and has more than 20 years of experience with linux and windows operating systems. He also writes for Biteno.com