In a Nutshell: What is Kali Linux Explained
Kali Linux is an open-source, Debian-based Linux distribution that is widely recognized for its robust penetration testing and security auditing capabilities. It is specifically designed to assist cybersecurity professionals in identifying and exploiting vulnerabilities in computer systems.
With over 600 pre-loaded penetration testing tools, Kali Linux provides a comprehensive arsenal for vulnerability management, computer forensics, and reverse engineering. Its extensive collection of specialized tools makes it a valuable resource for professionals in the cybersecurity field.
Kali Linux adheres to the Filesystem Hierarchy Standard and offers multi-language support, allowing users to tailor the distribution to their specific needs. It has comprehensive compatibility with wireless devices, enabling wireless network testing and analysis.
The development of Kali Linux is conducted in a secure environment, ensuring the integrity and authenticity of the distribution. The use of GPG signed packages and repositories adds an additional layer of security.
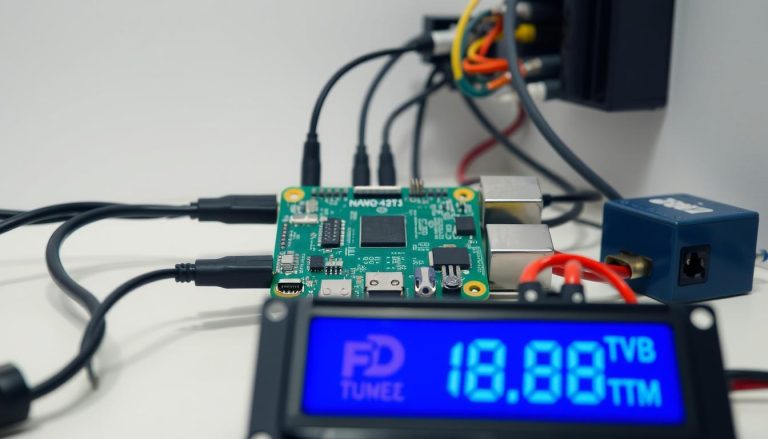
Furthermore, Kali Linux is compatible with ARM systems such as the Raspberry Pi and BeagleBone Black, expanding its potential usability and reach.
In conclusion, Kali Linux stands as a powerful and customizable Linux distribution that offers a wide range of tools for penetration testing, computer forensics, and reverse engineering. Its focus on security and extensive functionality make it an essential resource for cybersecurity professionals.
Key Takeaways:
- Kali Linux is a Debian-based Linux distribution designed for penetration testing and security auditing.
- It comes pre-loaded with over 600 specialized tools for vulnerability management, computer forensics, and reverse engineering.
- Kali Linux adheres to the Filesystem Hierarchy Standard and supports multi-language options.
- It has comprehensive compatibility with wireless devices, facilitating wireless network testing and analysis.
- Kali Linux offers a secure development environment with GPG signed packages and repositories.
- It is compatible with ARM systems, including popular devices like Raspberry Pi and BeagleBone Black.
Understanding Kali Linux’s Purpose and Features
Kali Linux serves as a powerful platform for conducting vulnerability management, computer forensics, and reverse engineering tasks, thanks to its extensive suite of pre-installed tools and comprehensive features. This open-source, Debian-based Linux distribution has gained popularity among cybersecurity professionals due to its specialized focus on advanced Penetration Testing and Security Auditing.
One of the key features of Kali Linux is its collection of over 600 penetration testing tools, making it a versatile resource for identifying and exploiting vulnerabilities in computer systems. From network analysis and password cracking to data recovery and malware analysis, Kali Linux covers a wide range of cybersecurity tasks, ensuring that professionals have the necessary tools at their disposal.
Furthermore, Kali Linux adheres to the Filesystem Hierarchy Standard, ensuring consistency and ease of use. Its custom kernel is patched for injection, providing comprehensive support for wireless devices and empowering users to conduct wireless network testing and analysis. The distribution also offers multi-language support, allowing users to customize their experience and work in their preferred language.
| Key Features of Kali Linux |
|---|
| 600+ pre-installed penetration testing tools |
| Filesystem Hierarchy Standard compliance |
| Custom kernel patched for injection |
| Comprehensive support for wireless devices |
| Multi-language support |
In addition, the development of Kali Linux is carried out in a secure environment, ensuring the integrity and authenticity of the distribution. The use of GPG signed packages and repositories further enhances security measures, instilling confidence in users that they are working with a trusted and reliable platform.
Kali Linux also extends its compatibility to ARM systems, making it suitable for devices like the Raspberry Pi and BeagleBone Black. This opens up new possibilities for cybersecurity enthusiasts and professionals looking to leverage Kali Linux’s capabilities in a portable and efficient manner.
Overall, Kali Linux’s purpose and features make it an invaluable tool for cybersecurity experts. Whether it’s identifying vulnerabilities, conducting digital investigations, or reverse engineering software and systems, Kali Linux provides the necessary resources to efficiently carry out these tasks.
An Overview of Kali Linux for Penetration Testing
Kali Linux is widely used by penetration testers due to its comprehensive range of tools specifically designed for identifying and exploiting vulnerabilities in computer systems. As an open-source, Debian-based Linux distribution, Kali Linux offers over 600 pre-installed penetration testing tools, making it a valuable resource in the field of cybersecurity.
One of the key features of Kali Linux is its focus on vulnerability management. With its extensive collection of specialized tools, penetration testers can effectively identify and assess security weaknesses in target systems, allowing organizations to strengthen their defenses and protect against potential threats.
Furthermore, Kali Linux provides powerful capabilities in the field of computer forensics. Its tools and techniques enable professionals to conduct thorough investigations, gather digital evidence, and analyze data to uncover crucial information. This makes Kali Linux an indispensable asset for forensic analysts in their mission to solve cybercrimes and address security breaches.
Another significant aspect of Kali Linux is its support for reverse engineering. With its comprehensive set of tools, professionals can analyze and understand the inner workings of software and systems, making it easier to detect vulnerabilities and develop effective countermeasures. Reverse engineering plays a crucial role in ensuring the security and integrity of computer systems, and Kali Linux provides the necessary tools to carry out this vital task.
| Key Features of Kali Linux for Penetration Testing |
|---|
| Comprehensive range of over 600 pre-installed penetration testing tools |
| Focus on vulnerability management |
| Powerful capabilities in computer forensics |
| Support for reverse engineering of software and systems |
In conclusion, Kali Linux is a highly regarded Linux distribution among penetration testers. Its wide array of tools, tailored for vulnerability management, computer forensics, and reverse engineering, make it an invaluable asset in the field of cybersecurity. Whether you are a security professional or an organization looking to bolster your defenses, Kali Linux provides the necessary resources to identify and address vulnerabilities, protect sensitive data, and ensure the security of computer systems.
Exploring the Key Tools in Kali Linux
Kali Linux boasts an extensive arsenal of penetration testing tools, including but not limited to network analysis, wireless testing, and password cracking utilities. These tools are specifically designed to assist cybersecurity professionals in identifying vulnerabilities and assessing the security of computer systems.
One notable tool in Kali Linux is Nmap, a powerful network scanning tool that allows users to discover hosts and services on a network, identify open ports, and gather information about the target. It provides a variety of scanning techniques, such as TCP connect scanning, SYN scanning, and UDP scanning. Nmap is widely recognized as an essential tool for network mapping and reconnaissance.
Another indispensable tool is Aircrack-ng, which is widely used for wireless network testing and analysis. It enables professionals to assess the security of Wi-Fi networks by capturing packets, testing their encryption strength, and cracking WEP and WPA/WPA2-PSK keys. Aircrack-ng supports various wireless adapters and offers advanced features like deauthentication attacks and fake access point creation.
Hydra is yet another powerful tool included in Kali Linux, specializing in online password attacks. It supports a wide range of protocols and services, including FTP, SSH, Telnet, HTTP, and many more. By leveraging Hydra’s efficient and customizable brute force and dictionary attack methods, cybersecurity professionals can evaluate the strength of user passwords and enhance overall system security.
| Tool | Purpose |
|---|---|
| Nmap | Network scanning and reconnaissance |
| Aircrack-ng | Wireless network analysis and security assessment |
| Hydra | Password cracking utility for various protocols |
Additional Tools
Aside from these three essential tools, Kali Linux provides a vast array of others, ranging from web application scanners like Burp Suite and OWASP ZAP, to vulnerability assessment tools like OpenVAS and Nexpose. There are also tools dedicated to computer forensics, such as Autopsy and Volatility, which assist in the investigation and analysis of digital evidence.
Kali Linux reinforces its position as a leading penetration testing distribution by continually updating and expanding its toolset. By offering such a comprehensive collection of powerful and specialized tools, Kali Linux equips cybersecurity professionals with the resources needed to effectively test and secure computer systems.
Getting Started with Kali Linux: A Step-by-Step Tutorial
This tutorial aims to help beginners navigate their way through the installation, configuration, and initial setup of Kali Linux, ensuring an optimal starting point for their cybersecurity journey.
Step 1: Downloading and Installing Kali Linux
- Visit the official Kali Linux website – www.kali.org
- Click on the “Downloads” tab and select the appropriate version for your system (32-bit or 64-bit)
- Once the download is complete, create a bootable USB drive using Etcher or Rufus
- Insert the USB drive into your computer and restart
- During the boot process, access the boot menu and select the USB drive as the boot device
- Follow the on-screen instructions to complete the installation
Step 2: Initial Configuration and Setup
Once the installation is complete, you will be prompted to configure some initial settings:
- Create a user account and set a strong password
- Choose your timezone and language preferences
- Configure network settings, such as Ethernet or Wi-Fi connections
- Update the system packages to ensure you have the latest security updates
Step 3: Exploring the Kali Linux Desktop
After completing the initial setup, you will be greeted with the Kali Linux desktop environment. Take some time to familiarize yourself with the various components:
- The application menu, located in the top left corner, provides access to all installed tools and utilities
- The taskbar, typically located at the bottom of the screen, displays open applications and system tray icons
- The panel on the right side of the screen contains useful widgets, such as a system monitor and a file manager
| Keyboard Shortcuts | Description | ||
|---|---|---|---|
|
Opens a terminal window | ||
|
Opens the application menu | ||
|
Opens the file manager |
“Kali Linux gives beginners the opportunity to dive into the exciting world of cybersecurity. By following this step-by-step tutorial, you can quickly set up your own Kali Linux environment and start exploring its powerful tools.”
Step 4: Getting Familiar with the Tools
Kali Linux comes pre-loaded with over 600 penetration testing tools. Although exploring all of them may seem daunting, it’s important to start with the basics:
- Begin with tools like Nmap for network scanning, Metasploit for vulnerability assessment, and Wireshark for packet analysis
- Read the official Kali Linux documentation and online tutorials to learn more about each tool
- Practice on virtual machines or test environments to avoid any unintended consequences
By following this tutorial and gradually expanding your knowledge, you can leverage the power of Kali Linux and embark on an exciting journey in the field of cybersecurity.
Where to Download Kali Linux
To download Kali Linux, you can visit the official website of the project or explore alternative sources, ensuring you have access to the most up-to-date version of the distribution. The official website, https://www.kali.org/, provides a straightforward and reliable method to download the latest release of Kali Linux. Here, you will find a variety of installation options, including ISO images for installation on physical hardware and virtual machine images for popular virtualization platforms like VMware and VirtualBox.
Additionally, the official website offers detailed documentation, guiding you through the installation process and providing valuable resources to help you get started with Kali Linux. The documentation covers a wide range of topics, including installation guides, user manuals, and tutorials.
If you prefer to explore alternative sources for downloading Kali Linux, you can find trusted mirrors listed on the official website. These mirrors are maintained by volunteers who ensure that the distribution files are up-to-date and accessible from various locations around the world. By choosing a mirror closer to your geographical location, you can potentially reduce download times and ensure a faster installation process.
Table: Official Download Options
| Option | Description |
|---|---|
| ISO Images | Full installation images for physical hardware |
| Virtual Machine Images | Pre-configured images for popular virtualization platforms |
| Netboot Images | Minimal bootable images for network installations |
| Live Images | Bootable images for testing and evaluation purposes |
Remember, when downloading Kali Linux, it is essential to verify the integrity of the downloaded files to ensure that they have not been tampered with. The official website provides instructions on how to verify the authenticity and integrity of the downloaded files using cryptographic signatures. By following these steps, you can be confident in the validity of your Kali Linux installation.
Navigating the Kali Linux Documentation
The Kali Linux documentation serves as a valuable resource for users, allowing them to gain a deeper understanding of the distribution’s features, tools, and methodologies. Whether you’re a beginner or an experienced cybersecurity professional, the documentation provides comprehensive guidance and support to help you make the most of Kali Linux.
One of the key features of the Kali Linux documentation is its organization and structure. The documentation is neatly categorized into different sections, covering everything from installation and basic configuration to advanced penetration testing techniques. This makes it easy to navigate and locate the specific information you’re looking for.
Additionally, the documentation is filled with detailed explanations, step-by-step tutorials, and practical examples. It provides insights into the intricacies of various tools and methodologies, allowing users to develop a solid understanding of how to effectively utilize Kali Linux in their cybersecurity endeavors.
Exploring the Official Documentation Sources
The official Kali Linux website serves as the primary source of documentation. It provides an extensive library of articles, guides, and tutorials that cover a wide range of topics. From understanding the basics of Kali Linux to mastering advanced penetration testing techniques, the official documentation has you covered.
| Documentation Source | Description |
|---|---|
| Kali Linux Official Website | The official website is a comprehensive resource that covers all aspects of Kali Linux, including installation, usage, and troubleshooting. |
| Kali Linux Forums | The forums provide a platform for users to interact, share knowledge, and seek help from the Kali Linux community. |
| Kali Linux Documentation GitHub | The documentation GitHub repository offers the latest updates, tutorials, and community-contributed content. |
In addition to the official sources, there are also numerous online forums, blogs, and video tutorials that can supplement your learning journey. These resources provide a wealth of knowledge and insights from cybersecurity professionals who have hands-on experience with Kali Linux.
By harnessing the power of the Kali Linux documentation, you can enhance your understanding of the distribution’s capabilities, master advanced techniques, and become a more proficient cybersecurity practitioner.
Kali Linux and its Compatibility with Wireless Devices
Kali Linux provides extensive support for a wide range of wireless devices, enabling professionals to perform comprehensive wireless network testing and analysis. With its custom kernel patched for injection, Kali Linux ensures that users have the necessary tools and functionalities to assess the security of wireless networks.
One of the key features of Kali Linux is its ability to work with popular wireless interfaces, such as Wi-Fi adapters and Bluetooth devices. This compatibility allows cybersecurity professionals to conduct various tests, including sniffing and capturing network traffic, testing network vulnerabilities, and assessing the effectiveness of encryption protocols.
To assist users in navigating the intricacies of wireless network testing, Kali Linux offers a variety of pre-installed tools. These tools include airodump-ng for capturing packets, aireplay-ng for packet injection, and airmon-ng for managing wireless interfaces. These tools, combined with Kali Linux’s extensive documentation, empower professionals to perform in-depth analysis and secure wireless networks effectively.
| Tool Name | Description |
|---|---|
| airodump-ng | A packet capture and analysis tool for wireless networks. |
| aireplay-ng | A packet injection tool used for testing network vulnerabilities. |
| airmon-ng | A tool for managing wireless interfaces and monitoring network traffic. |
Whether it’s assessing the security of a Wi-Fi network or conducting advanced wireless penetration testing, Kali Linux offers professionals the tools and support needed to confidently analyze and secure wireless environments.
Customizability and Multi-Language Support in Kali Linux
Kali Linux offers users the flexibility to customize and personalize the distribution to suit their specific requirements, making it a versatile platform for cybersecurity professionals worldwide. With its extensive range of tools and features, users can tailor their Kali Linux experience to enhance productivity and efficiency.
One of the standout features of Kali Linux is its multi-language support. This means that users have the option to work with the distribution in their preferred language, allowing for a more seamless and intuitive user experience. Whether it’s English, Spanish, French, or any other supported language, users can navigate through the interface, access tools, and read documentation in their chosen language.
Furthermore, Kali Linux provides users with the ability to customize the desktop environment, allowing for a personalized workflow. Users can choose from a range of desktop environments such as GNOME, KDE, Xfce, or i3, depending on their preferences and requirements. This level of customization extends to the overall look and feel of the distribution, giving users the freedom to create a personalized and efficient working environment.
Additionally, Kali Linux supports the use of custom repositories, allowing users to access additional tools and packages not included in the default installation. This flexibility enables users to expand their arsenal of cybersecurity tools and stay up to date with the latest advancements in the field.
Customizability and Multi-Language Support in Kali Linux – Table Summary
| Feature | Description |
|---|---|
| Multi-Language Support | Kali Linux provides support for multiple languages, allowing users to work in their preferred language for a more intuitive experience. |
| Customizable Desktop Environment | Users have the ability to customize the desktop environment, choosing from a range of options to suit their preferences and workflow. |
| Custom Repositories | Kali Linux supports the use of custom repositories, enabling users to access additional tools and packages beyond the default installation. |
Kali Linux Development and Security Measures
The development of Kali Linux is conducted in a secure environment, with the use of GPG signed packages and repositories, providing users with confidence in the integrity and security of the distribution. This approach ensures that the software has not been tampered with and that users can trust the authenticity of the packages they install.
Kali Linux follows the Filesystem Hierarchy Standard, which ensures consistency and compatibility across different Linux distributions. This adherence allows users to easily navigate and interact with the file system, making it convenient to manage and customize their Kali Linux installation.
| Key Security Measures | Benefits |
|---|---|
| GPG Signed Packages and Repositories | Ensures the integrity and authenticity of the software |
| Secure Development Environment | Prevents unauthorized access and reduces the risk of vulnerabilities |
| Regular Updates and Patching | Keeps the distribution up to date with the latest security enhancements |
Additionally, Kali Linux’s development team actively maintains and updates the distribution, ensuring that it remains secure and up to date. The regular release of updates and patches addresses any discovered vulnerabilities and provides users with a reliable and secure platform.
Overall, the development and security measures implemented in Kali Linux allow users to confidently use the distribution for penetration testing, computer forensics, reverse engineering, and other cybersecurity tasks. The combination of a secure development environment, GPG signed packages and repositories, and regular updates ensures the trustworthiness and reliability of Kali Linux.
Kali Linux on ARM Systems: Raspberry Pi and BeagleBone Black
Kali Linux extends its versatility by providing support for ARM systems, allowing users to deploy the distribution on devices like the Raspberry Pi and BeagleBone Black. This compatibility opens up a world of possibilities for cybersecurity professionals and enthusiasts who want to explore Kali Linux’s tools and features on small, portable platforms.
One of the notable advantages of running Kali Linux on ARM systems is the ability to conduct penetration testing and security auditing on embedded devices. With the Raspberry Pi and BeagleBone Black, users can assess the security of IoT devices, network routers, and other ARM-based systems. Kali Linux’s extensive collection of tools, combined with the power and flexibility of these ARM devices, makes for a formidable combination in the world of cybersecurity.
Moreover, Kali Linux ensures a seamless user experience on ARM systems. The distribution is optimized to take full advantage of the unique capabilities and architecture of ARM processors. This optimization results in improved performance and efficiency, allowing users to execute various security tasks with ease.
| Kali Linux on ARM Systems | Key Benefits |
|---|---|
| Compatibility with Raspberry Pi | Enables security testing on IoT devices and other ARM-based systems |
| Compatibility with BeagleBone Black | Offers a portable platform for penetration testing and security auditing |
| Optimized Performance | Utilizes the full potential of ARM processors for efficient security tasks |
By embracing the ARM architecture, Kali Linux expands its reach beyond traditional desktop and server environments. This compatibility with devices like the Raspberry Pi and BeagleBone Black empowers individuals and organizations to enhance their understanding of cybersecurity and develop innovative solutions for securing ARM-based systems.
Leveraging Kali Linux for Computer Forensics
Kali Linux provides professionals in the field of computer forensics with a robust set of tools and methodologies for conducting thorough digital investigations and analysis. Whether it’s recovering deleted data, examining system logs, or analyzing network traffic, Kali Linux offers a comprehensive suite of forensic tools that can help uncover critical evidence in a forensic examination.
One of the key advantages of Kali Linux for computer forensics is its vast collection of specialized tools. These tools cover a wide range of forensic techniques, including file system analysis, memory forensics, and network forensics. With tools like The Sleuth Kit, Autopsy, Volatility, Wireshark, and many others, forensic professionals have everything they need to delve deep into digital evidence and extract valuable information.
| Tool | Description |
|---|---|
| The Sleuth Kit | A collection of command-line tools for file system analysis and digital investigation. |
| Autopsy | A graphical interface for The Sleuth Kit, providing an intuitive way to navigate and analyze digital evidence. |
| Volatility | An advanced memory forensics framework that allows for the analysis of volatile memory dumps. |
| Wireshark | A powerful network protocol analyzer that enables deep inspection of network traffic. |
In addition to the extensive toolset, Kali Linux also offers a highly customizable environment. Forensic professionals can tailor the distribution to their specific needs by installing additional tools, creating custom scripts, and configuring the system according to their workflow. This flexibility allows for greater efficiency and productivity during investigations.
By leveraging Kali Linux’s comprehensive set of tools and the customizable environment, professionals in the field of computer forensics can conduct in-depth investigations, uncover hidden evidence, and present compelling findings. Kali Linux continues to be a go-to choice for forensic professionals due to its extensive capabilities and ongoing development by the cybersecurity community.
The Power of Kali Linux in Reverse Engineering
Kali Linux empowers professionals in the field of reverse engineering by providing them with a comprehensive set of tools and methodologies to analyze and dissect software and systems. With its vast collection of specialized tools, Kali Linux enables professionals to delve deep into the inner workings of applications and uncover vulnerabilities, making it an indispensable resource in the world of cybersecurity.
One of the key features of Kali Linux for reverse engineering is its support for disassemblers and decompilers. Tools such as Radare2 and Ghidra allow users to examine the assembly code of binaries and understand how they function at a low level. By decompiling the code, professionals can gain insights into the logic and functionality of the software, making it easier to identify potential weaknesses.
In addition to disassemblers and decompilers, Kali Linux also offers powerful debugging tools like GDB and ltrace. These tools allow professionals to analyze the execution of a program, track memory usage, and identify any issues or vulnerabilities. By stepping through the code and examining the state of variables and registers, reverse engineers can gain a deeper understanding of how the software operates and uncover any hidden functionalities or security flaws.
Furthermore, Kali Linux provides support for static and dynamic analysis tools, such as IDA Pro and Burp Suite. These tools enable professionals to analyze the behavior of software in real-time and identify potential vulnerabilities. By simulating various scenarios and inputs, reverse engineers can assess the security of the software and develop strategies to mitigate any potential risks.
| Key Tools for Reverse Engineering in Kali Linux |
|---|
| 1. Radare2 – A powerful disassembler and debugger |
| 2. Ghidra – An open-source software reverse engineering suite |
| 3. GDB – The GNU Project debugger for analyzing program execution |
| 4. ltrace – A debugging and profiling utility for tracking library calls |
| 5. IDA Pro – A widely-used interactive disassembler |
| 6. Burp Suite – A comprehensive web application security testing tool |
In conclusion, Kali Linux offers a powerful arsenal of tools and methodologies for professionals engaged in reverse engineering. Its extensive collection of disassemblers, decompilers, debuggers, and analysis tools enables users to uncover vulnerabilities, understand software behavior, and develop effective security strategies. With its open-source nature and strong community support, Kali Linux continues to be a go-to platform for reverse engineers in their quest to analyze and secure software and systems.
Unleashing the Potential: Kali Linux’s Customizability and Beyond
Kali Linux’s customizability empowers users to tailor the distribution to suit their unique preferences and requirements, further enhancing their cybersecurity endeavors. With its open-source nature and a wide range of customization options, Kali Linux allows users to create a personalized and efficient environment for their penetration testing, computer forensics, and reverse engineering tasks.
One of the key aspects of Kali Linux’s customizability is its vast collection of over 600 penetration testing tools that come pre-loaded with the distribution. These tools cover various aspects of cybersecurity, including vulnerability management, wireless network testing, and digital investigations. Users can easily organize and prioritize these tools based on their specific needs, ensuring a streamlined and targeted approach to their work.
Additionally, Kali Linux provides support for multi-language environments, allowing users from different regions and backgrounds to work comfortably in their native languages. It also adheres to the Filesystem Hierarchy Standard, ensuring compatibility and ease of use for users coming from other Linux distributions.
Kali Linux Customization Options
Users can further enhance their Kali Linux experience by customizing various aspects of the distribution. They have the flexibility to modify the graphical user interface, adapt the command-line environment to their preferences, and customize the built-in tools based on their workflow.
Furthermore, Kali Linux offers compatibility with a range of wireless devices, including popular platforms like Raspberry Pi and BeagleBone Black. This opens up new possibilities for users to conduct wireless network assessments and experiment with different hardware configurations.
In conclusion, Kali Linux’s customizability allows users to shape the distribution according to their specific cybersecurity needs. With its extensive collection of tools, multi-language support, and compatibility with wireless devices, Kali Linux provides a powerful platform for professionals in the field. By harnessing the potential of customization, users can maximize their productivity and effectiveness in various cybersecurity tasks.
| Key Features | Benefits |
|---|---|
| Over 600 pre-loaded penetration testing tools | Efficient and streamlined workflow |
| Adherence to Filesystem Hierarchy Standard | Compatibility with other Linux distributions |
| Multi-language support | Inclusion and ease of use for diverse user base |
| Customizable user interface and command-line environment | Personalized user experience |
| Compatibility with wireless devices | Expanded possibilities for wireless network testing |
Conclusion
Kali Linux’s advanced capabilities, extensive toolset, and robust security measures make it an indispensable asset for cybersecurity professionals, enabling them to conduct effective penetration testing, computer forensics, and reverse engineering tasks. This open-source, Debian-based Linux distribution is specifically tailored for these specialized fields, providing over 600 pre-loaded penetration testing tools.
With Kali Linux, professionals can efficiently manage vulnerabilities, conduct comprehensive digital investigations, and analyze the inner workings of software and systems. It adheres to the Filesystem Hierarchy Standard and offers a custom kernel patched for injection, ensuring compatibility with various wireless devices and enabling wireless network testing and analysis.
The development of Kali Linux is carried out in a secure environment, with GPG signed packages and repositories, ensuring the integrity and authenticity of the distribution. It also boasts multi-language support, allowing users to customize the distribution to their specific needs and preferences.
Kali Linux goes beyond its extensive toolset and customizable features by providing support for ARM systems like the Raspberry Pi and BeagleBone Black. This broad compatibility further expands its potential applications and versatility in different hardware environments.
FAQ
What is Kali Linux?
Kali Linux is an open-source, Debian-based Linux distribution that focuses on advanced Penetration Testing and Security Auditing.
What are the key features of Kali Linux?
Kali Linux comes pre-loaded with over 600 penetration testing tools, offers comprehensive support for wireless devices, and includes a custom kernel patched for injection.
What is the purpose of Kali Linux?
Kali Linux is tailored for tasks such as vulnerability management, computer forensics, and reverse engineering.
Is Kali Linux free?
Yes, Kali Linux is free and open-source.
Does Kali Linux support ARM systems like Raspberry Pi and BeagleBone Black?
Yes, Kali Linux has support for ARM systems, including popular devices like Raspberry Pi and BeagleBone Black.
How is the development of Kali Linux secured?
The development of Kali Linux is done in a secure environment, with GPG signed packages and repositories.
Can Kali Linux be customized?
Yes, Kali Linux is highly customizable, allowing users to tailor the distribution to their specific needs.
- About the Author
- Latest Posts
Janina is a technical editor at Text-Center.com and loves to write about computer technology and latest trends in information technology. She also works for Biteno.com.