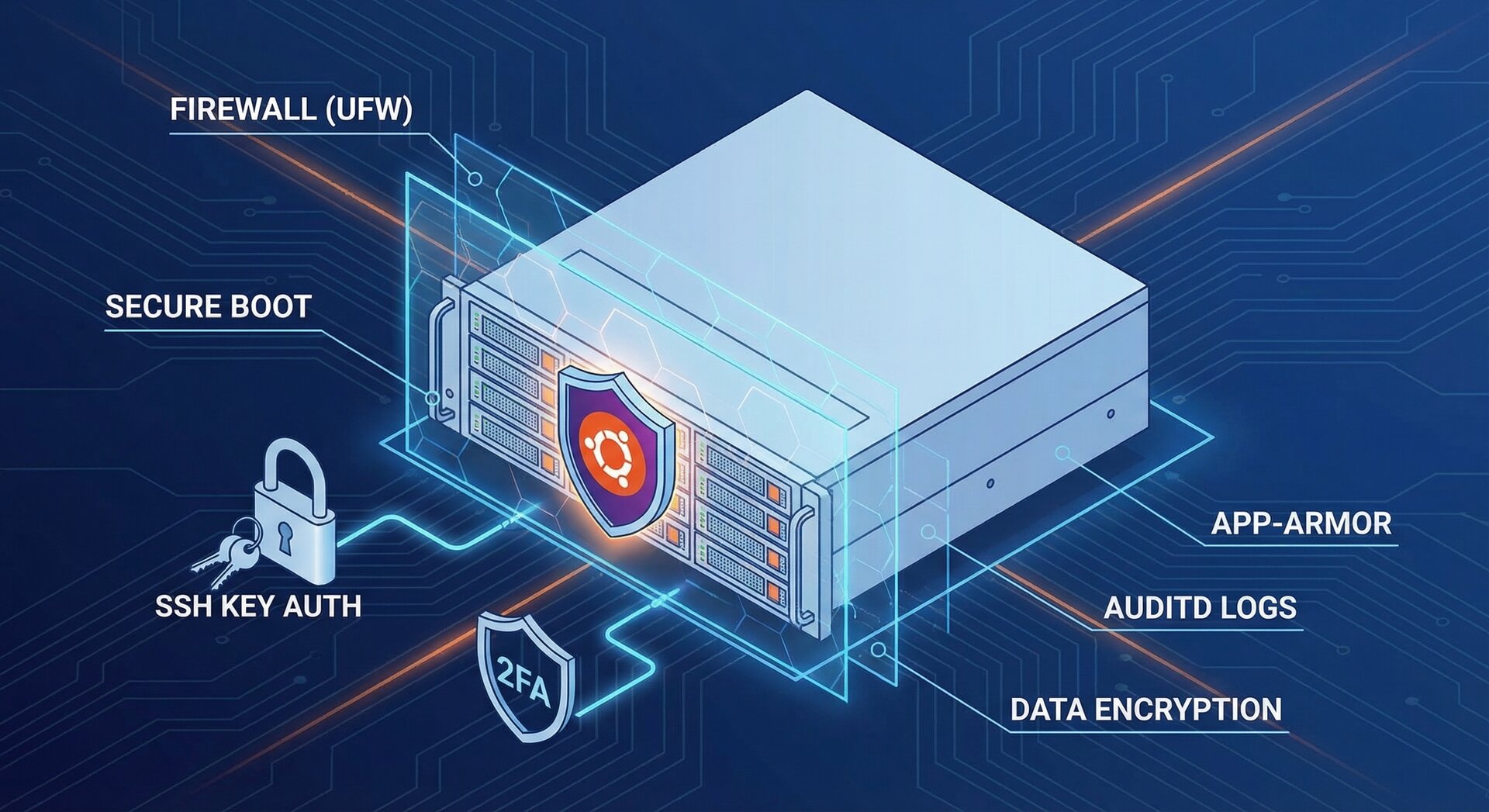
How to Secure Ubuntu Server 2026: Complete Security Hardening Guide
Learning how to secure ubuntu server installations is critical for protecting your infrastructure in 2026. With cyber threats evolving rapidly, implementing comprehensive security hardening measures isn’t optional—it’s essential. This complete guide walks you through proven strategies to secure ubuntu server deployments, from SSH configuration to firewall management and automated patch deployment.
Whether you’re managing a single VPS or multiple production servers, these battle-tested techniques will help you build a robust security posture that withstands modern attack vectors.
Why Ubuntu Server Security Matters in 2026
The threat landscape has intensified dramatically. Automated scanning tools continuously probe exposed servers for vulnerabilities, making security hardening your first line of defense. When you properly secure ubuntu server systems, you reduce your attack surface by 80-90% according to recent security audits.
Ubuntu’s popularity makes it a frequent target. Attackers exploit default configurations, weak SSH settings, and unpatched systems. A hardened server configuration prevents most automated attacks before they reach your applications.
Step 1: Implement Strong User Management and Access Control
The foundation to secure ubuntu server infrastructure starts with proper user management. Running services as root is one of the most dangerous practices still seen in production environments.
Create a Non-Root Administrative User
Always create a dedicated user account with sudo privileges instead of using the root account directly:
2
sudo usermod -aG sudo secureadmin
This approach provides accountability through audit trails. Every sudo command is logged with the username, timestamp, and executed command. When multiple administrators access your system, you can track exactly who did what.
Disable Root Login
After setting up your administrative user, disable direct root login entirely. Edit
|
1
|
/etc/ssh/sshd_config
|
and set:
This single change eliminates the most privileged account from remote access attempts. Attackers cannot brute-force the root password if root login is disabled.
Remove Unnecessary User Accounts
Regularly audit your user accounts and remove those no longer needed. Former employees, test accounts, and abandoned service users represent security liabilities:
The
|
1
|
–remove-home
|
flag ensures all user data is deleted, preventing data leaks from inactive accounts.
Step 2: Harden SSH Configuration for Maximum Security
SSH hardening is crucial when you want to secure ubuntu server remote access. Default SSH configurations are functional but not secure for production use.
Disable Password Authentication
Password-based authentication is vulnerable to brute-force attacks. Switch to SSH key authentication exclusively:
2
PubkeyAuthentication yes
Generate strong SSH keys using modern algorithms:
The Ed25519 algorithm provides excellent security with small key sizes. The
|
1
|
-a 100
|
parameter increases key derivation function rounds for added protection against offline attacks.
Change the Default SSH Port
While security through obscurity isn’t a primary defense, changing the default SSH port (22) significantly reduces automated scan traffic:
Most automated scanners target port 22 exclusively. Moving to a non-standard port reduces log noise and CPU cycles wasted on blocked connection attempts. For enhanced strategies on protecting automation scripts, check out our guide on Linux shell scripting security best practices 2026.
Limit Authentication Attempts
Configure SSH to disconnect after a limited number of failed authentication attempts:
2
LoginGraceTime 30
These settings prevent brute-force attacks from running indefinitely. After three failed attempts, the connection is terminated.
Disable Unnecessary SSH Features
Most servers don’t need X11 forwarding, TCP forwarding, or agent forwarding. Disable these features unless specifically required:
2
3
AllowTcpForwarding no
AllowAgentForwarding no
Each disabled feature reduces potential attack vectors. The principle of least privilege applies to protocol features as well as user permissions.
Use Strong Cryptographic Algorithms
Configure SSH to use only modern, secure algorithms:
2
3
Ciphers [email protected],[email protected],[email protected]
MACs [email protected],[email protected]
These settings eliminate weak legacy algorithms while maintaining compatibility with modern SSH clients. The ChaCha20-Poly1305 cipher offers excellent performance on systems without AES hardware acceleration.
Manage Idle Connections
Configure SSH to terminate idle connections automatically:
2
ClientAliveCountMax 2
This configuration sends keepalive messages every 300 seconds (5 minutes). If the client doesn’t respond after two attempts, the connection is closed. This prevents abandoned sessions from remaining open indefinitely.
Step 3: Configure and Enable UFW Firewall
A properly configured firewall is essential to secure ubuntu server network access. Ubuntu’s Uncomplicated Firewall (UFW) provides a user-friendly interface to iptables.
Enable UFW with Essential Rules
Before enabling UFW, ensure you allow SSH connections or you’ll lock yourself out:
2
3
4
sudo ufw default deny incoming
sudo ufw default allow outgoing
sudo ufw enable
This configuration denies all incoming connections except those explicitly allowed. Outgoing connections are permitted by default, allowing your server to initiate connections for updates and external API calls.
Application-Specific Rules
Add rules for your specific services:
2
sudo ufw allow 443/tcp comment 'HTTPS'
The comment parameter helps document why each rule exists, crucial for future maintenance.
Rate Limiting for SSH
Enable rate limiting to prevent brute-force SSH attacks:
UFW’s limit rule blocks IP addresses that attempt more than 6 connections within 30 seconds. This automatic throttling stops most automated brute-force attempts.
Learn more about comprehensive firewall strategies from Ubuntu’s official security documentation.
Step 4: Install and Configure Fail2ban
While UFW provides network-level filtering, Fail2ban adds intelligent intrusion prevention by monitoring log files and automatically blocking suspicious IP addresses.
Install Fail2ban
2
sudo apt install fail2ban -y
Configure SSH Jail
Create a local configuration file:
Add SSH protection:
2
3
4
5
6
enabled = true
port = 2222
maxretry = 3
bantime = 3600
findtime = 600
This configuration bans IP addresses for one hour after three failed login attempts within 10 minutes. Adjust these values based on your security requirements and user base.
Start and Enable Fail2ban
2
sudo systemctl start fail2ban
Monitor banned IPs with:
Step 5: Implement Automated Patch Management
Unpatched systems are the leading cause of successful server compromises. Implementing automated security updates is critical to secure ubuntu server infrastructure long-term.
Enable Unattended Upgrades
2
sudo dpkg-reconfigure --priority=low unattended-upgrades
Configure automatic security updates in
|
1
|
/etc/apt/apt.conf.d/50unattended-upgrades
|
:
2
3
4
5
"${distro_id}:${distro_codename}-security";
};
Unattended-Upgrade::Automatic-Reboot "true";
Unattended-Upgrade::Automatic-Reboot-Time "03:00";
This configuration automatically installs security updates and reboots the server at 3 AM if required. Schedule reboots during your lowest-traffic period.
Maintain System Inventory
Keep an accurate inventory of all Ubuntu systems, their versions, and installed packages. This inventory is foundational for effective patch management at scale.
Tools like Ansible, Puppet, or AWS Systems Manager can automate patch deployment across multiple servers. For detailed patch management strategies, refer to Action1’s Ubuntu patch management guide.
Test Updates Before Production Deployment
Always test updates in a staging environment before applying them to production systems. While security updates are critical, they can occasionally cause compatibility issues with specific applications.
Step 6: Monitor System Performance and Security
Continuous monitoring helps you detect security incidents and performance issues before they become critical problems.
Essential Metrics to Monitor
Track these key indicators:
- CPU Usage: Sudden spikes may indicate compromised processes or cryptomining malware
- Memory Consumption: Memory leaks or malicious processes consume resources over time
- Disk Usage: Rapidly filling disks can indicate log flooding or unauthorized data storage
- Network Traffic: Unusual outbound traffic patterns suggest data exfiltration
- Running Processes: Unknown processes are immediate red flags
Review System Logs Regularly
Check authentication logs for suspicious activity:
Review system logs for errors:
The
|
1
|
-p err
|
parameter filters for error-level messages, while
|
1
|
-b
|
shows only messages from the current boot.
Set Up Automated Alerts
Configure email notifications for critical security events. Tools like logwatch can send daily summary reports of system activity.
Step 7: Additional Security Hardening Measures
Beyond the core configurations, implement these additional measures to secure ubuntu server deployments comprehensively.
Keep the Full Application Stack Updated
Don’t limit updates to the operating system. Update web servers (Apache, Nginx), databases (MySQL, PostgreSQL), container engines (Docker), and all application dependencies regularly.
Implement Proper Filesystem Permissions
Follow the principle of least privilege for file permissions:
2
sudo find /var/www -type f -exec chmod 644 {} \;
Web directories should be readable but not writable by the web server process unless specifically required for uploads or caches.
Enable AppArmor
AppArmor provides mandatory access control (MAC) to restrict program capabilities. Ubuntu ships with AppArmor enabled and several default profiles. Ensure it’s active:
Implement Regular Backup Strategies
Security hardening protects against attacks, but backups protect against everything else—hardware failures, accidental deletions, and successful breaches that require system restoration.
Implement the 3-2-1 backup rule: three copies of data, on two different media types, with one copy off-site. Test backup restoration regularly.
Use Security Scanning Tools
Regularly scan your server for vulnerabilities:
2
sudo lynis audit system
Lynis performs comprehensive security audits and provides actionable recommendations for improving your security posture. For additional security analysis tools, check out LinuxSecurity’s hardening best practices.
Conclusion: Building a Secure Ubuntu Server Foundation
Learning how to secure ubuntu server systems requires implementing multiple layers of defense. No single technique provides complete protection, but combining user management, SSH hardening, firewall configuration, intrusion prevention, automated patching, and continuous monitoring creates a robust security posture.
Start with SSH hardening and firewall configuration—these provide immediate security improvements. Then implement automated updates and monitoring to maintain security over time. Regular security audits with tools like Lynis help identify weaknesses before attackers exploit them.
Remember that security is an ongoing process, not a one-time configuration. As threats evolve and new vulnerabilities are discovered, continuously update your security practices to secure ubuntu server infrastructure effectively throughout 2026 and beyond.
Further Reading
- Official Ubuntu Security Updates
- Center for Internet Security (CIS)
- More Linux Tutorials on HowTo-Do.it
- Server Management Guides
- About the Author
- Latest Posts
Mark is a senior content editor at Text-Center.com and has more than 20 years of experience with linux and windows operating systems. He also writes for Biteno.com