Understanding the Basics: What is a Hypervisor?
I am often asked to explain complex concepts in simple terms. Today, I want to shed some light on the topic of hypervisors and help you understand what they are and how they work. So, what is a hypervisor? In simple terms, a hypervisor is computer software or hardware that allows you to host multiple virtual machines. It acts as a mediator between the physical hardware and the virtual machines, providing each virtual machine with its own set of resources while appearing to have access to the host hardware.
Key Takeaways:
- A hypervisor is computer software or hardware that enables hosting of multiple virtual machines.
- There are two main types of hypervisors: Type 1 (bare metal) and Type 2 (hosted).
- Type 1 hypervisors run directly on the hardware and are commonly used in enterprise data centers.
- Type 2 hypervisors run on top of an operating system and are more suited for individual users.
- Hypervisors expand hardware capabilities, improve system reliability and security, and enable remote work scenarios.
Types of Hypervisors: A Closer Look
In the world of virtualization technology, hypervisors play a crucial role in enabling the creation and management of virtual machines. There are two main types of hypervisors: Type 1 (bare metal) and Type 2 (hosted). Each type has its own advantages and use cases.
Type 1 Hypervisors
Type 1 hypervisors, also known as bare metal hypervisors, run directly on the hardware without the need for an underlying operating system. They provide superior performance and security, making them ideal for enterprise data centers. Examples of Type 1 hypervisors include VMware ESXi and Microsoft Hyper-V.
Type 2 Hypervisors
Type 2 hypervisors, on the other hand, run on top of an operating system. They are more suitable for individual users and offer greater flexibility and compatibility with a wide range of hardware. Examples of Type 2 hypervisors include Oracle VirtualBox and VMware Workstation.
Both types of hypervisors allow for the virtualization of resources such as CPU, memory, and storage. They enable the execution of multiple operating systems on a single piece of hardware, providing the ability to create and manage virtual machines effectively.
To further understand the different types of hypervisors, let’s take a closer look at the comparison table below:
| Type of Hypervisor | Key Features | Examples |
|---|---|---|
| Type 1 (Bare Metal) | Run directly on hardware Superior performance and security Ideal for enterprise data centers |
VMware ESXi Microsoft Hyper-V |
| Type 2 (Hosted) | Run on top of an operating system Greater flexibility and compatibility More suitable for individual users |
Oracle VirtualBox VMware Workstation |
This table provides a clear overview of the key differences between Type 1 and Type 2 hypervisors. It highlights their unique features and showcases their specific use cases. Understanding these differences is essential when choosing the right hypervisor for your virtualization needs.
Benefits of Hypervisors in Virtualization
Hypervisors have revolutionized the field of virtualization technology, offering a range of benefits that enhance hardware capabilities, control IT-related costs, and improve system reliability and security. By efficiently allocating and reallocation resources to virtual machines, hypervisors expand the capabilities of hardware, enabling the execution of multiple operating systems on a single piece of hardware.
One of the key advantages of hypervisors is their ability to control IT-related costs. By virtualizing resources such as CPU, memory, and storage, hypervisors allow for efficient utilization of hardware, maximizing its potential and reducing the need for additional physical infrastructure. This not only saves costs on hardware procurement but also streamlines maintenance and management efforts.
Furthermore, hypervisors provide improved system reliability and security. Each virtual machine operates in its own isolated environment, with its own dedicated resources, while appearing to have access to the host hardware. This isolation ensures that any issues or failures in one virtual machine do not affect others, resulting in enhanced system reliability. Additionally, the isolation provided by hypervisors adds an extra layer of security, preventing unauthorized access to critical resources and protecting sensitive data.
Benefits of Hypervisors in Virtualization
- Expanded hardware capabilities
- Controlled IT-related costs
- Improved system reliability
- Enhanced system security
In summary, hypervisors play a crucial role in virtualization technology, offering a multitude of benefits such as expanded hardware capabilities, controlled IT-related costs, improved system reliability, and enhanced system security. By leveraging the power of hypervisors, organizations can optimize their infrastructure, improve operational efficiency, and ensure a secure and reliable computing environment.
How Hypervisors Work: Under the Hood
Understanding how hypervisors work is essential to grasp their role in virtualization and virtual machine management. Hypervisors are responsible for the efficient allocation of resources and the isolation of virtual machines. Let’s dive into the inner workings of hypervisors and explore how they operate.
When a hypervisor is running, it loads the client operating systems of virtual machines and allocates the necessary CPU resources, memory, bandwidth, and disk storage space. This process ensures that each virtual machine has its own dedicated resources, providing the appearance of dedicated hardware while utilizing the capabilities of the host system.
To effectively manage these resources, hypervisors employ various techniques such as resource allocation and scheduling. They monitor resource usage by virtual machines, ensuring fair distribution and preventing any one virtual machine from monopolizing resources. Hypervisors also enable virtual machines to make requests through API calls, enabling communication between the virtual machine and the hypervisor.
Overall, hypervisors play a crucial role in the successful execution and management of virtual machines. They allow for the efficient allocation of resources, enable isolation between virtual machines, and facilitate communication through API calls. Understanding how hypervisors work under the hood is essential for harnessing the power of virtualization and leveraging the benefits it offers.
Hypervisor Operation
| Component | Functionality |
|---|---|
| Virtual Machine Load | The hypervisor loads the client operating systems of virtual machines, enabling them to run on the host system. |
| Resource Allocation | The hypervisor allocates CPU resources, memory, bandwidth, and disk storage space to each virtual machine, ensuring fair distribution. |
| Resource Monitoring | The hypervisor monitors resource usage by virtual machines, preventing resource monopolization and optimizing resource utilization. |
| Scheduling | The hypervisor manages the scheduling of resources, ensuring efficient utilization and preventing conflicts between virtual machines. |
| API Calls | Virtual machines make requests to the hypervisor through API calls, enabling communication and interaction between the virtual machine and the hypervisor. |
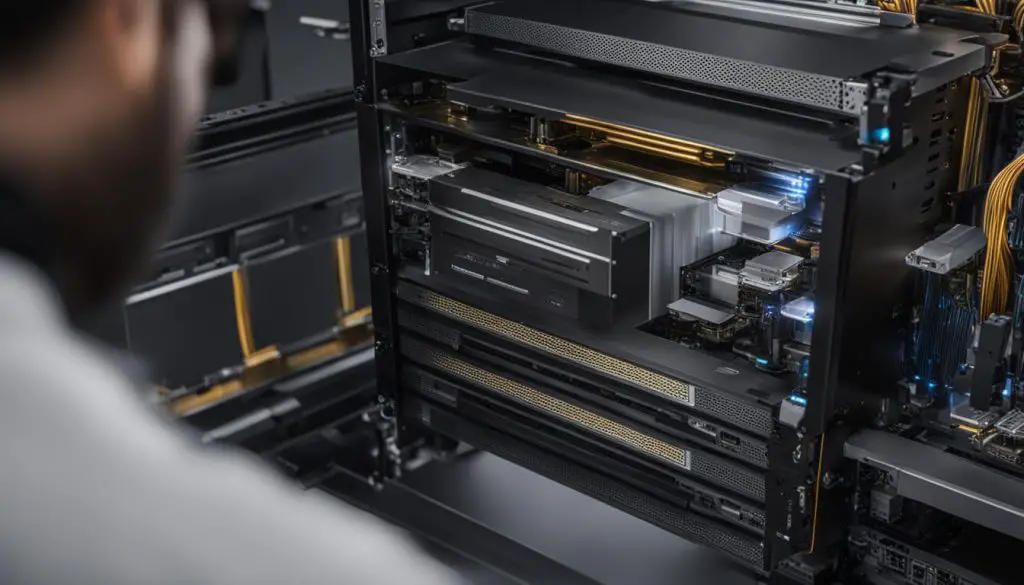
Bare Metal vs Hosted Hypervisors: Choosing the Right One
When selecting a hypervisor for your virtualization needs, one of the most important decisions to make is whether to go with a bare metal hypervisor or a hosted hypervisor. Each option has its own strengths and considerations that should be taken into account.
The Advantages of Bare Metal Hypervisors
Bare metal hypervisors, such as VMware ESXi and Microsoft Hyper-V, offer superior performance and security. As they run directly on the hardware, they have direct access to resources and can optimize hardware utilization. This makes them a popular choice for enterprise data centers where performance and security are critical.
Bare metal hypervisors also provide a level of isolation and independence from the underlying operating system, which can reduce the risk of conflicts and vulnerabilities. Additionally, they offer advanced features like live migration and high availability, allowing for seamless workload management and minimizing downtime.
The Benefits of Hosted Hypervisors
On the other hand, hosted hypervisors, such as Oracle VirtualBox and VMware Workstation, are more user-friendly and easier to set up. They run on top of an operating system, which makes them compatible with a wide range of hardware and allows for the convenient management of virtual machines.
Hosted hypervisors are a great choice for individual users or small-scale virtualization needs. They offer the flexibility of running multiple operating systems on a personal computer and provide a user-friendly interface for managing virtual machines. They are also a cost-effective solution as they do not require dedicated hardware resources.
| Bare Metal Hypervisors | Hosted Hypervisors | |
|---|---|---|
| Performance | Superior | Good |
| Security | High | Good |
| Hardware Optimization | Yes | No |
| User-Friendliness | Requires technical expertise | Easy to use |
“Bare metal hypervisors offer superior performance and security, making them ideal for enterprise data centers. Hosted hypervisors, on the other hand, are more user-friendly and suitable for individual users or small-scale virtualization needs.”
Ultimately, the choice between bare metal and hosted hypervisors depends on your specific requirements and use case. If performance and security are paramount, and you have the technical expertise to manage dedicated hardware resources, a bare metal hypervisor may be the best option. However, if ease of use and compatibility with a wide range of hardware are more important, a hosted hypervisor can provide the flexibility and convenience you need.
It’s important to evaluate your virtualization needs and consider the performance, security, hardware optimization, and user-friendliness of each hypervisor type before making a decision. By carefully weighing the advantages and disadvantages, you can choose the right hypervisor that meets your specific requirements and provides the best virtualization experience.
Hypervisors and Containers: Similarities and Differences
When it comes to virtualization, there are two popular options: hypervisors and containers. While both serve the purpose of isolating computing environments, they have distinct characteristics and use cases. Let’s take a closer look at the similarities and differences between hypervisors and containers.
Similarities
- Hypervisors and containers both provide isolation for running applications and processes.
- Both allow for the efficient utilization of resources, such as CPU, memory, and storage.
- They offer scalability, enabling applications to be easily deployed and scaled across multiple instances.
- Both hypervisors and containers provide a level of portability, allowing applications to be moved or replicated across different environments.
Differences
Containers are lightweight and share the host operating system, making them more efficient and faster to start compared to hypervisors. They are limited to running a single type of operating system, which can be an advantage in scenarios where application compatibility is crucial. On the other hand, hypervisors allow for the emulation of entire servers, OSs, desktops, and networks. They have their own operating system, which provides increased resources but also adds complexity.
Containers are often used in environments where scalability and rapid deployment are key, such as cloud-native applications. They are well-suited for microservices architecture, where applications are broken down into smaller, independent components. Hypervisors, on the other hand, are more suitable for resource-intensive functions and scenarios that require running multiple operating systems on a single machine, such as server virtualization.

In Summary
In summary, while both hypervisors and containers serve the purpose of isolating computing environments, they have different strengths and use cases. Containers offer lightweight, scalable, and portable solutions, ideal for cloud-native applications and microservices architecture. Hypervisors, on the other hand, provide the ability to emulate entire servers and are well-suited for resource-intensive tasks and scenarios that require running multiple operating systems. Understanding the similarities and differences between hypervisors and containers is crucial in choosing the right virtualization technology for your specific needs.
Hypervisors and Security: The Role in Cloud Computing
When it comes to cloud computing, hypervisors play a crucial role in ensuring the security and integrity of the virtualized environment. As the underlying software or hardware layer that enables the creation and management of virtual machines, hypervisors have access to all hardware resources and are responsible for managing the execution of virtual machines.
However, this very nature also makes hypervisors a potential target for hackers who may exploit vulnerabilities in the hypervisor software or attempt to gain unauthorized access to the virtual machines running on the system. It is therefore essential to implement robust security measures to protect against these threats.
Industry guidelines and best practices provide valuable guidance in enhancing hypervisor security. One such example is the Virtualization Security Guidelines published by the National Institute of Standards and Technology (NIST). These guidelines outline recommended security controls and considerations for virtualization environments, including hypervisor security.
Hypervisor Vulnerabilities and Mitigation
Like any software, hypervisors can have vulnerabilities that may be exploited by attackers. These vulnerabilities can range from memory corruption issues to privilege escalation exploits. To mitigate these risks, hypervisor providers such as Microsoft and VMware continuously work to identify and address potential vulnerabilities through regular security updates and patches.
“It is crucial to keep hypervisor software up to date with the latest security patches and updates to reduce the risk of exploitation.”
In addition to keeping the hypervisor software up to date, network configuration and planning also play a critical role in ensuring hypervisor security. By implementing proper network segmentation and access controls, organizations can limit the exposure of the hypervisor to potential threats and isolate virtual machines from each other.
Virtualization Security Best Practices
Adhering to industry best practices is essential for maintaining a secure virtualization environment. Alongside keeping hypervisor software up to date, organizations should implement strong access controls and authentication mechanisms to prevent unauthorized access. Regular security audits and vulnerability assessments should also be conducted to identify and address any potential security weaknesses.
By following industry guidelines, staying informed about the latest security vulnerabilities, and implementing robust security measures, organizations can mitigate the risks associated with hypervisor security in cloud computing environments. This ensures the confidentiality, integrity, and availability of data and resources in the virtualized environment, providing a secure foundation for cloud-based operations.
Hypervisors for Desktop Virtualization: Enabling Remote Work
As the global workforce continues to embrace remote work, the demand for flexible and accessible solutions has grown exponentially. Hypervisors have emerged as a crucial tool in enabling desktop virtualization, allowing employees to access their virtual desktops from any location. By leveraging hypervisors, organizations can provide seamless remote work experiences, regardless of the physical location of employees.
With desktop virtualization, hypervisors host virtual desktops on a server, replicating the functionality and appearance of physical desktops. This means that employees can access their PCs remotely through virtual desktop infrastructure (VDI) solutions. Whether working from home, a coffee shop, or a client’s office, employees can connect to their virtual desktops securely over the internet, enabling them to work with the same applications, files, and settings they have on their physical desktops.
Desktop virtualization powered by hypervisors offers numerous benefits. It enhances accessibility by enabling employees to work from any device, including laptops, tablets, and smartphones. This flexibility empowers individuals to choose the device that best suits their needs and preferences while maintaining a consistent user experience. Additionally, desktop virtualization improves data security as sensitive information remains centralized on the server, minimizing the risk of data loss or breaches caused by lost or stolen devices.
Furthermore, hypervisors ensure the scalability and manageability of virtual desktop environments. IT administrators can easily provision, update, and manage virtual desktops from a centralized location, reducing the complexity and time required for traditional desktop management. This streamlines IT operations and enables organizations to efficiently scale their remote work capabilities in response to changing business needs.
Benefits of Hypervisors for Desktop Virtualization:
- Enables remote work by providing access to virtual desktops from anywhere
- Replicates the functionality and appearance of physical desktops
- Enhances accessibility by enabling work from any device
- Improves data security by centralizing sensitive information on servers
- Facilitates scalability and manageability of virtual desktop environments
By leveraging hypervisors for desktop virtualization, organizations can unlock the full potential of remote work. Employees gain the flexibility to work from anywhere, choosing the devices that suit their needs, while organizations benefit from enhanced data security and streamlined IT operations. As businesses continue to adapt to the changing landscape of work, hypervisors will play a crucial role in enabling remote work and ensuring productivity and business continuity.
Hypervisors and Cloud Computing Security: Mitigating Risks
When it comes to cloud computing security, hypervisors play a crucial role in ensuring the integrity of virtualized environments. However, like any software, they can have vulnerabilities that can be exploited by malicious actors. To mitigate these risks and maintain a secure cloud computing environment, several measures can be taken.
Secure APIs
One of the key aspects to consider is the use of secure APIs (Application Programming Interfaces) between the hypervisor and other components of the cloud infrastructure. Secure APIs help to prevent unauthorized access and ensure that communication between different parts of the system is encrypted and authenticated.
Network Planning
Proper network planning is another crucial factor in mitigating hypervisor vulnerabilities. By carefully designing network architecture, including setting up firewalls, implementing network segmentation, and employing intrusion detection and prevention systems, the risk of unauthorized access and lateral movement within the cloud environment can be minimized.
Industry Guidelines
Adhering to industry guidelines and best practices is also essential for protecting against hypervisor vulnerabilities. Organizations should follow established security frameworks and standards, such as NIST’s Virtualization Security Guidelines, which provide recommendations for securing virtualized environments. These guidelines cover various aspects, including hypervisor hardening, secure virtual machine management, and secure virtual machine migration.
By implementing secure APIs, conducting thorough network planning, and following industry guidelines, organizations can significantly enhance the security of their cloud computing environments. It is important to regularly review and update security measures to stay ahead of emerging threats and ensure the continued protection of sensitive data and resources.
Table: Best Practices for Mitigating Hypervisor Vulnerabilities
| Best Practice | Description |
|---|---|
| Implement secure APIs | Use secure APIs to ensure authenticated and encrypted communication between the hypervisor and other components of the cloud infrastructure. |
| Conduct network planning | Design a robust network architecture, including firewalls, network segmentation, and intrusion detection/prevention systems, to minimize unauthorized access and lateral movement. |
| Follow industry guidelines | Adhere to industry security guidelines, such as NIST’s Virtualization Security Guidelines, for best practices in securing virtualized environments. |
| Regularly review and update | Continuously assess and update security measures to address emerging threats and maintain the security of cloud computing environments. |
Conclusion
In conclusion, hypervisors are essential components of virtualization, enabling the hosting and management of multiple virtual machines. With different types available, such as bare metal and hosted hypervisors, businesses and individuals have the flexibility to choose the right solution for their specific needs.
By expanding hardware capabilities and providing efficient resource allocation, hypervisors improve system reliability and security. They also play a critical role in enabling remote work scenarios through desktop virtualization, allowing employees to access their virtual desktops from anywhere.
While hypervisors are crucial for cloud computing, it is important to address their security vulnerabilities. Following industry guidelines, incorporating secure APIs, and conducting careful network planning can help mitigate risks and ensure the overall security of cloud computing environments.
With continuous advancements and a focus on adhering to security protocols, hypervisors serve as a solid foundation for virtualization and cloud computing, offering enhanced capabilities, reliability, and security for businesses and individuals alike.
FAQ
What is a hypervisor?
A hypervisor is computer software or hardware that enables you to host multiple virtual machines.
What are the types of hypervisors?
There are two types of hypervisors: Type 1 (bare metal) and Type 2 (hosted).
How do Type 1 hypervisors differ from Type 2 hypervisors?
Type 1 hypervisors run directly on the hardware, while Type 2 hypervisors run on top of an operating system.
What are the benefits of hypervisors in virtualization?
Hypervisors expand hardware capabilities, improve system reliability and security, and help control IT-related costs.
How do hypervisors work?
Hypervisors load client operating systems of virtual machines and allocate the necessary resources.
What is the difference between bare metal and hosted hypervisors?
Bare metal hypervisors run directly on the hardware and offer superior performance and security, while hosted hypervisors are easier to set up and compatible with a wider range of hardware.
How do hypervisors compare to containers?
Containers are lightweight and scalable, while virtual machines have their own operating systems and provide increased resources.
What is the role of hypervisors in cloud computing security?
Hypervisors play a crucial role in controlling resources and managing virtual machines, but they can also be vulnerable to security threats.
How can hypervisor vulnerabilities be mitigated?
Hypervisor security can be improved by following industry guidelines, utilizing secure APIs, and careful network planning.
How are hypervisors used in desktop virtualization for remote work?
Hypervisors enable the creation and management of virtual desktops, allowing employees to work remotely and access their PCs over the Internet.
- About the Author
- Latest Posts
Mark is a senior content editor at Text-Center.com and has more than 20 years of experience with linux and windows operating systems. He also writes for Biteno.com